With IoT security taking center stage in global technology discussions, the Cyber Resilience Act (CRA) has emerged as a critical regulatory framework that cannot be overlooked. Why is there a sudden spotlight on CRA now? Are other certifications now becoming obsolete?
"The EU Cyber Resilience Act (EU CRA) entered into force on December 10, 2024. EU CRA implementation strengthens the cybersecurity of products with digital elements (PDEs) placed in the EU market by introducing mandatory cybersecurity requirements for manufacturers."
Here is a detailed deep dive into the latest trends in the IoT security domain and the growing traction of CRA in the IoT industry, especially in the European market.
What is the EU Cyber Resilience Act?
The EU Cyber Resilience Act (EU CRA) entered into force on December 10, 2024. EU CRA implementation strengthens the cybersecurity of products with digital elements (PDEs) placed in the EU market by introducing mandatory cybersecurity requirements for manufacturers. Under the EU CRA regulation, all software and hardware products with digital elements that connect to a network should meet the mandatory cybersecurity requirements from the design and development stage, and handle vulnerability patches during the entire lifecycle of the product.

Several IoT security regulations have already been introduced globally to improve device security and compliance. Frameworks such as the EU CE RED certification, the US Cyber Trust Mark, and the Network and Information Security Directive (NIS) have been in place for some time and continue to guide manufacturers in building secure connected devices.
The latest framework gaining significant traction on this list is the EU Cyber Resilience Act, or CRA.
CRA is the rulebook that guides manufacturers on how software and hardware devices should be designed, updated, and maintained to protect end customers. Under the CRA, some product categories may need third-party conformity assessment by notified bodies, while others may be assessed through self-assessment, depending on the product category and the standards applied.
Why is the Cyber Resilience Act crucial for IoT security?
In today's digital landscape, the threat landscape for connected devices is evolving rapidly. The CRA provides a much-needed framework that ensures these devices meet stringent security standards throughout their lifecycle, from design to deployment to patching. The focus on cybersecurity is essential to reduce vulnerabilities and safeguard data and privacy.
IoT devices, which are deeply integrated into our daily lives, need to be protected against a growing number of cyber threats. Whether it is a sensor, gateway, or cloud service, each component of the IoT ecosystem is a potential target for cyber-attacks. The CRA's proactive approach to IoT security establishes a consistent standard for manufacturers to follow, which helps reduce the overall risks in the IoT supply chain.
Given that many of the IoT devices are connected to sensitive environments, such as healthcare, finance, or critical infrastructure, the CRA ensures that they remain resilient in the face of increasing cyber threats.
Why are Cybersecurity Certifications in IoT Security a Non-Negotiable?
Cybersecurity certifications for IoT devices are evolving from a best practice to a legal mandate. In this scenario, what is the importance of cybersecurity certifications in IoT devices?
The advantages of IoT certifications for manufacturers include:
- Marketing differentiation: Certified products or those undergoing certification tend to receive more attention than uncertified products.
- Ahead of the curve: Planning for certification in advance avoids rushed work when deadlines approach and mitigates potential delays in time-to-market.
- Customer Trust: Achieving IoT certifications throughout the product development lifecycle builds customer trust and improves market penetration.
The Importance of IoT Cybersecurity Certifications
IoT cybersecurity certifications go beyond testing a product. They represent an integrated approach, starting right from consulting to understand the product’s intended ecosystem, followed by testing, reporting, certification assistance, and more.
What Manufacturers Need to Know About the EU Cyber Resilience Act (EU CRA)?
The Cyber Resilience Act (CRA) is a new EU regulation, with over 130 articles and 4 annexes, to ensure that hardware and software products with digital elements are designed, developed, and maintained in line with mandatory cybersecurity requirements.
Earlier, vulnerability-handling obligations were often defined by company policy or sector-specific requirements and were commonly limited to a fixed support period (typically 5 years).
The CRA puts forward a secure-by-design approach for all software and hardware products, making it compulsory by law.
Manufacturers are now required to address vulnerabilities and support product security for the declared support period, the expected lifetime of the product, or a minimum of five years, whichever is longer. Non-compliance with this will result in monetary penalties for manufacturers.
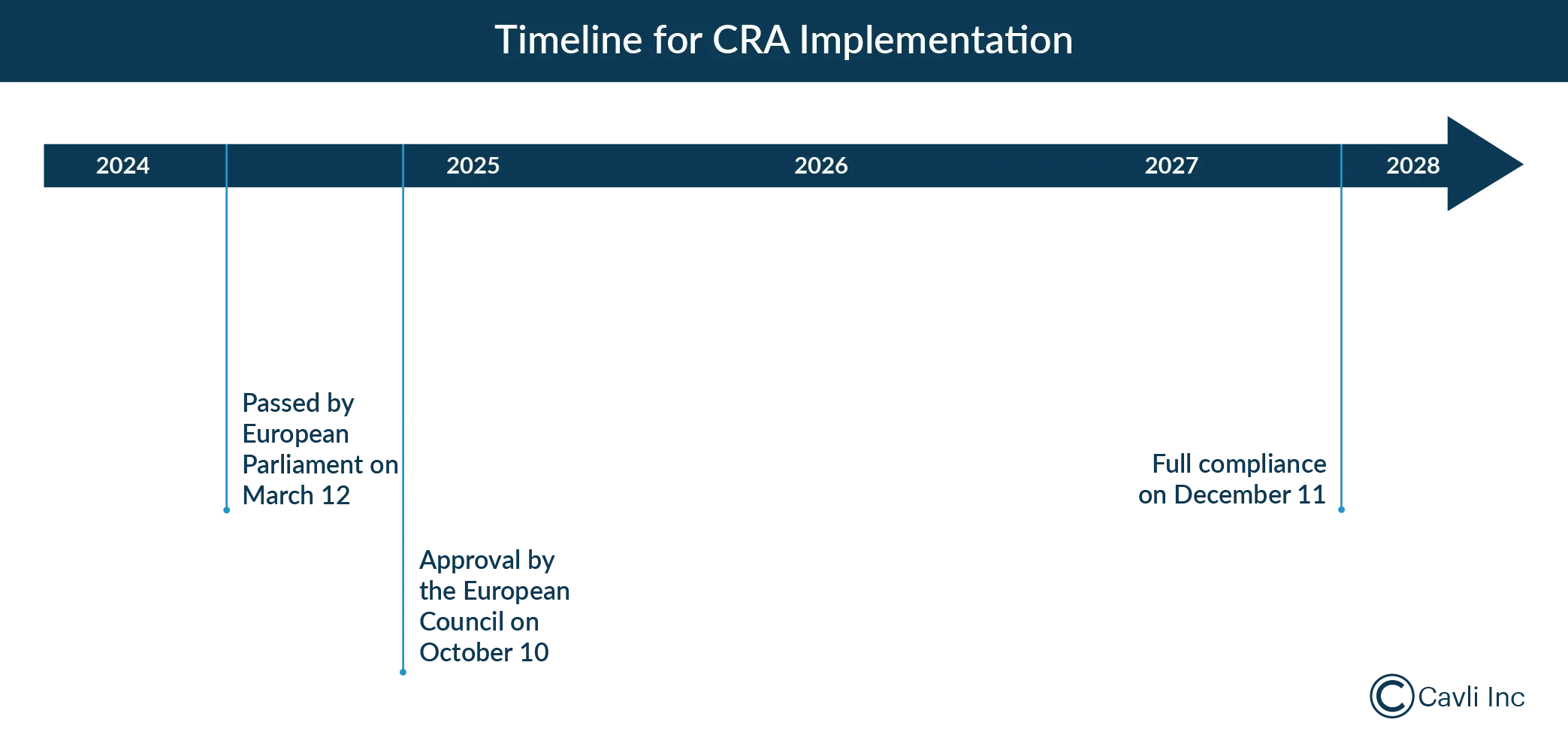
The first mandatory reporting date for manufacturers to comply with CRA is 11 September 2026, when actively exploited vulnerabilities and severe incidents must be reported to the relevant CSIRT via the CRA Single Reporting Platform. Complete CRA compliance is required by 11 December 2027, and the realistic roadmap advises beginning preparation for this transition at least 18 months in advance.
EU Cyber Resilience Act (EU CRA) Requirements and Their Impact on Cybersecurity
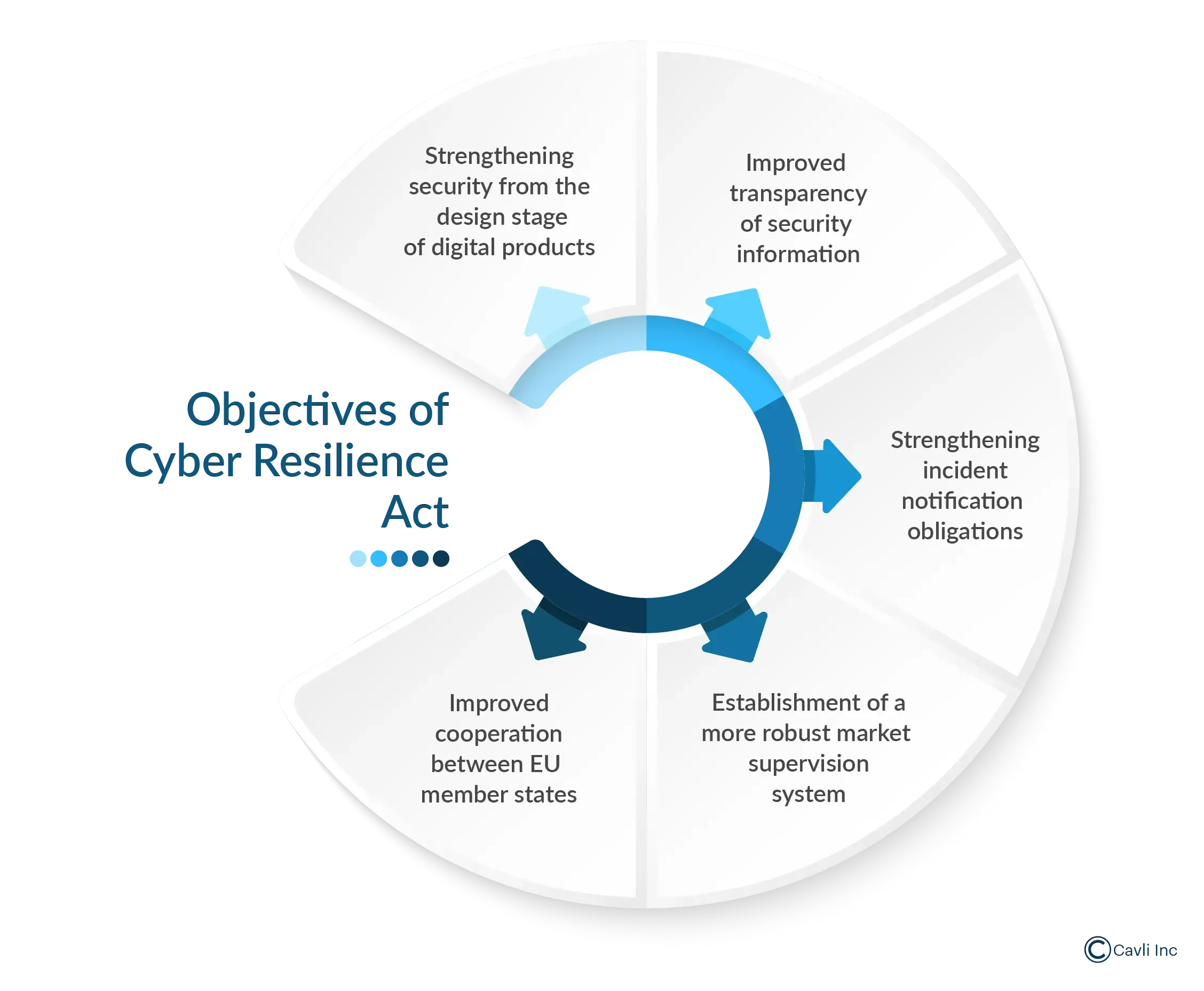
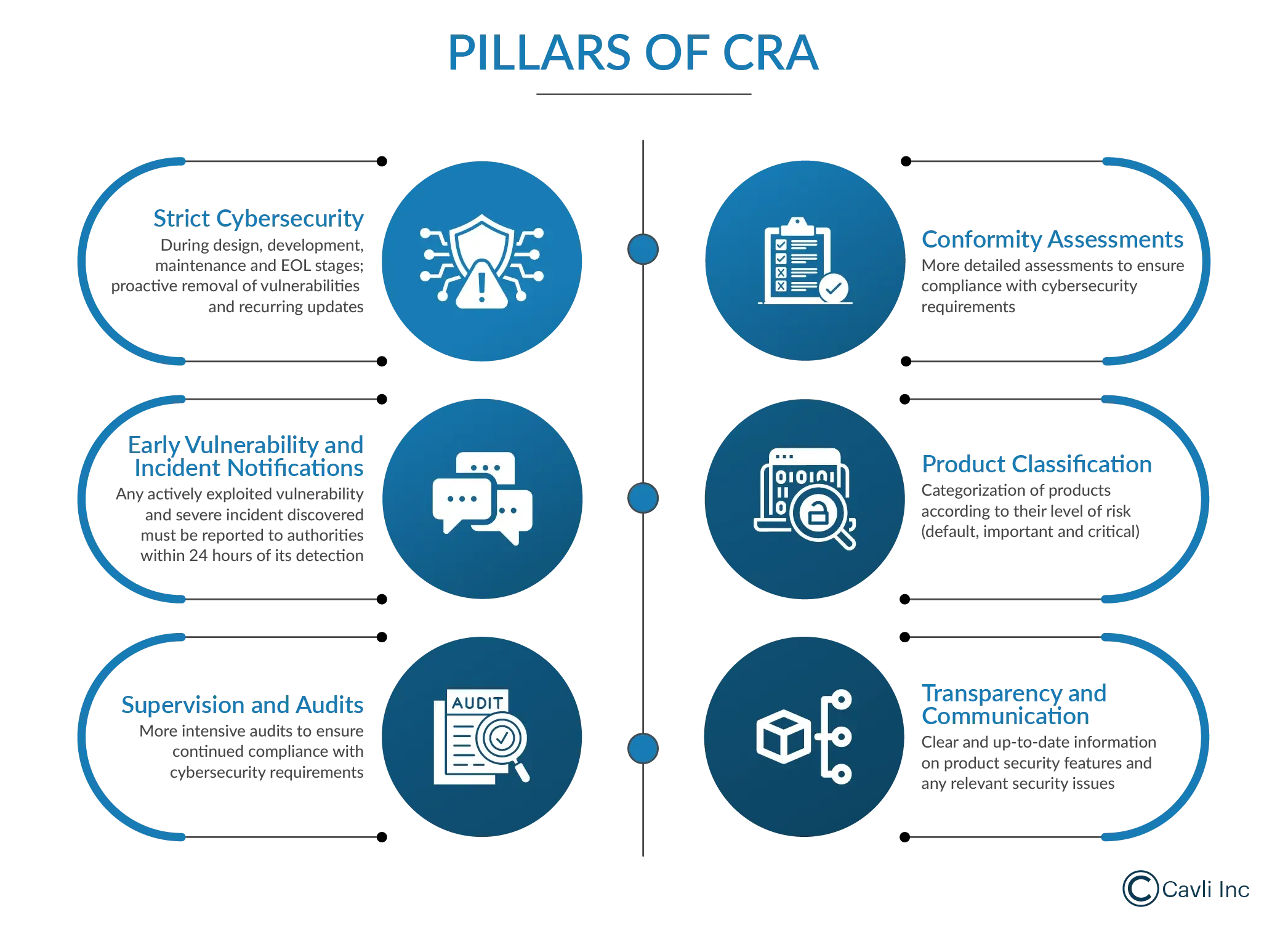
The Cyber Resilience Act (CRA) requirements outline several key components to enhance cybersecurity for digital products. These components include:
| Category | Key Items in EU CRA |
|---|---|
| Risk Assessments | Conduct mandatory cybersecurity risk assessments and ongoing vulnerability testing. |
| Security Requirements | Implement secure-by-design practices (e.g., encryption, MFA, threat modeling). |
| Vulnerability Reporting | Promptly report and address vulnerabilities with clear documentation. |
| Security Updates | Provide free security updates for at least five years, or the product's expected usage period if shorter. |
| Penalties | Fines up to €15 million or 2.5% of global turnover for non-compliance. |
| SBOM Transparency | Maintain a detailed inventory of software components to identify and mitigate risks. |
| Continuous Risk Mitigation | Regular penetration testing and real-time threat monitoring throughout the product lifecycle. |
| Supply Chain Transparency | Ensure third-party suppliers follow secure cybersecurity practices. |
Secure by design
At the design stage, manufacturers implement secure-by-design practices to reduce cybersecurity threats. This includes threat modeling, access controls (e.g., MFA), data encryption, secure communication protocols (TLS, VPN), and continuous penetration testing. Additionally, minimizing third-party dependencies and enabling OTA updates ensures ongoing security throughout the product lifecycle.
Comprehensive documentation
Comprehensive documentation is critical in the Cyber Resilience Act (CRA) because it ensures full transparency and accountability throughout the product lifecycle. It involves documenting threat models, vulnerability logs, risk assessments, and mitigation strategies in detail. It enables manufacturers to demonstrate compliance with regulatory requirements and provides a clear audit trail for cybersecurity decisions made during design, development, and post-release.
Software Bill of Materials (SBOM) transparency
Software Bill of Materials (SBOM) Transparency plays a crucial role in Cyber Resilience Act (CRA) compliance by providing an in-depth, detailed inventory of all software components, libraries, and dependencies used within a product. With a full SBOM, manufacturers can identify software dependencies (e.g., libraries or packages) that could introduce security risks. SBOM transparency accelerates the response time when new threats or vulnerabilities emerge and allows for the application of fixes without delay.
Continuous risk assessment and mitigation
Continuous Vulnerability Assessment and Mitigation requires manufacturers to integrate ongoing security testing throughout the product lifecycle. This includes regular penetration testing, static/dynamic analysis, and real-time threat monitoring. Identified vulnerabilities are logged, prioritized, and mitigated with patches or updates, ensuring products remain secure against emerging threats and minimizing risks from newly discovered vulnerabilities over time.
Supply chain transparency
Supply Chain Transparency requires manufacturers to gain full visibility into the cybersecurity practices of all third-party suppliers involved in the product’s development, including hardware, software, and service providers. The goal is to minimize risks that could arise from vulnerabilities introduced by external partners, whether through components, code, or outsourced services.
The Intersection of EU CRA, NIS2, and RED: A Unified Approach to EU Cybersecurity Compliance
EU Radio Equipment Directive (RED)
The EU Radio Equipment Directive (RED), adopted in 2014, regulates the placement of radio and telecommunications equipment on the European market to ensure it meets essential health, safety, and electromagnetic compatibility (EMC) requirements. It applies to a wide range of products, including smartphones, IoT devices, and wireless communication equipment. The directive ensures that these products do not cause harmful interference with other electronic devices and meet standards for radio frequency (RF) performance.
RED requires manufacturers to conduct conformity assessments and affix the CE mark to demonstrate compliance. It also mandates that devices include clear instructions and information on safe usage. Additionally, the directive ensures that end users are protected from the potential risks posed by electromagnetic radiation and guarantees that devices are compatible with EU-wide radio spectrum policies.
Network and Information Security Directive (NIS)
The NIS Directive (Network and Information Systems Directive), introduced in 2016, was the first EU-wide regulation aimed at improving cybersecurity for essential services and digital infrastructure. It focused on sectors critical to public health, safety, and the economy, such as energy, transport, banking, healthcare, and water supply. Under NIS, companies in these sectors must adhere to specific security requirements and report cyber incidents within a set timeframe.
The NIS2 Directive, adopted in 2020, builds on and strengthens the original NIS framework. It broadens the scope to include medium and large organizations in both essential services and digital services, like cloud providers and online marketplaces. NIS2 introduces stricter incident reporting timelines, more robust risk management practices, and penalties for non-compliance, including monetary fines of up to €10 million or 2% of global annual turnover. Non-monetary penalties may include corrective actions and public disclosures of security failures, aiming to enhance cybersecurity resilience across the EU.
EU RED vs NIS vs CRA Regulation
| Aspect | Radio Equipment Directive (RED) | Network and Information Security Directive (NIS) | CRA (Cyber Resilience Act) |
|---|---|---|---|
| Enforced on | June 2016 | January 2023 | December 2027 (partial enforcement by 11 June 2026) |
| Primary Focus | Safety and electromagnetic compatibility of radio and telecommunications equipment | Cybersecurity for critical infrastructure and digital services | Cyber resilience of connected devices and software, and protection from cyber risks |
| Scope | Applies to radio and telecommunications equipment (e.g., IoT devices) sold in the EU | Applies to operators of essential services (OES) and digital service providers (DSPs) | Applies to all connected devices and services in the EU market, focusing on security |
| Main Requirements | - Product safety - Electromagnetic compatibility - Radio spectrum compliance | - Risk management - Incident reporting - Security of networks and information systems | - Cybersecurity risk management - Requirements for vulnerability reporting - Product security for connected devices |
| Targeted Entities | Manufacturers of radio equipment and telecom devices | Critical infrastructure and digital service providers (e.g., energy, transport, health sectors) | Manufacturers and distributors of connected products and software |
| Cybersecurity Requirements | Limited to safety and electromagnetic compliance | Yes, addresses cyber risk management and incident reporting | Yes, focuses heavily on cyber resilience and protection against cyber threats |
| Key Compliance Aspects | Conformity assessments, CE marking, and product testing for safety and compliance | Risk assessment, security controls for services, incident handling | Vulnerability management, security updates, cyber resilience testing for products |
| Penalties | Penalties for non-compliance (restrictions on market entry) | Penalties for non-compliance (fines and sanctions) | Penalties for non-compliance (fines, bans on sale of non-compliant products) |
| Cybersecurity Framework | Not focused on cybersecurity, but safety and compliance | Addresses cyber resilience through risk management | Directly targets cybersecurity for IoT devices and software |
| Cyber Incident Response | No specific focus on incident response or cybersecurity incidents | Requires incident reporting within a certain timeframe | Requires cybersecurity incident reporting and vulnerability management |
Key Requirements for Achieving CRA Compliance: A Step-by-Step Guide
Product Categorization in the EU CRA
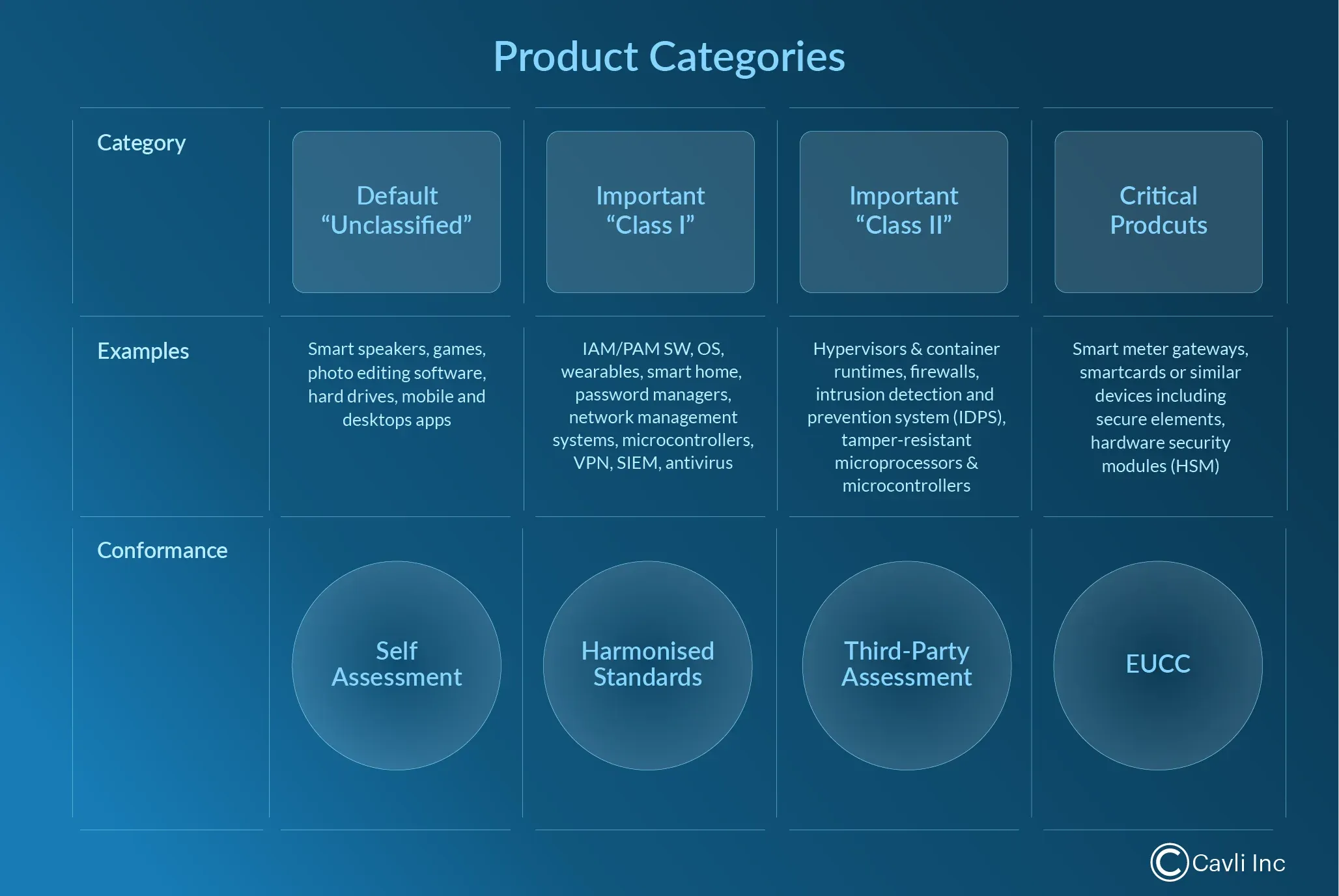
- Non-Critical Products
- These are products with lower cybersecurity risk profiles associated with their digital elements. Examples include:
- Hard drives
- Toys
- Photo editors
- Word processors
- These are products with lower cybersecurity risk profiles associated with their digital elements. Examples include:
- Important Products
- Class I Products: Products that manage sensitive operations or data, such as:
- Identity management systems
- Biometric readers
- Password managers
- Virtual private networks (VPNs)
- Network management systems
- Class II Products: Products for more critical security tasks, including:
- Hypervisors
- Industrial firewalls
- Tamper-resistant microcontrollers
- Class I Products: Products that manage sensitive operations or data, such as:
- Critical Products
- These include products with high-security requirements, and the examples are:
- Hardware Security Modules (HSM)
- Smart meter gateways
- Devices for advanced cryptographic functions
- These include products with high-security requirements, and the examples are:
This classification helps manufacturers and regulators apply different security requirements depending on the product’s level of risk, ensuring stronger protection for higher-risk products.
Cybersecurity Risk Assessment
The Cyber Resilience Act (CRA) requirements mandate that manufacturers conduct a cybersecurity risk assessment before launching their products. This process is designed to identify potential cybersecurity threats and vulnerabilities. Manufacturers are required to document these risks, assess potential impacts, and implement appropriate security measures to mitigate identified vulnerabilities.
The risk assessment must cover:
- Product security from design through the entire lifecycle.
- Vulnerability management to ensure that vulnerabilities are discovered, reported, and addressed promptly.
- Compliance with technical documentation requirements, providing end users with security information, and safety guidelines.
This approach ensures that products placed on the market are secure, reducing the risk of cyberattacks and improving overall cyber resilience within the EU's digital ecosystem.
Product Documentation
According to the EU Cyber Resilience Act (EU CRA), manufacturers of IoT products must enhance their product documentation to include comprehensive security and compliance information throughout the product's lifecycle. The documentation requirements include:
Technical Documentation
This must cover relevant cybersecurity details, such as identified vulnerabilities, third-party information, and updates to the risk assessment.
Conformity Declaration
This document demonstrates the product's compliance with essential cybersecurity requirements.
User Instructions
These guides must provide clear, understandable instructions for safe installation, operation, and usage, ensuring users and authorities can easily follow security protocols.
All documentation must be retained for at least 10 years or the duration of the product's support period, whichever is longer, ensuring transparency, accountability, and continued security compliance throughout the product's lifecycle.
Vulnerability Reporting and Handling
The EU Cyber Resilience Act (EU CRA) mandates that manufacturers implement structured procedures for vulnerability reporting and handling, which is a crucial aspect of maintaining cybersecurity in IoT products. The key elements of this process include:
Vulnerability Identification & Monitoring
Continuous monitoring for potential vulnerabilities, including regular assessments and security scans, is required. This includes both internal systems and third-party components.
Log Maintenance
Manufacturers must maintain detailed logs of identified vulnerabilities, actions taken, and communications in line with the CRA’s retention requirements.
Escalation Metrics
Vulnerabilities must be categorized and escalated according to their risk severity.
Vulnerability Disclosure to ENISA
When a vulnerability is detected, manufacturers should notify through the CRA Single Reporting Platform to the relevant CSIRT, with the information made available to ENISA, within specified timeframes.
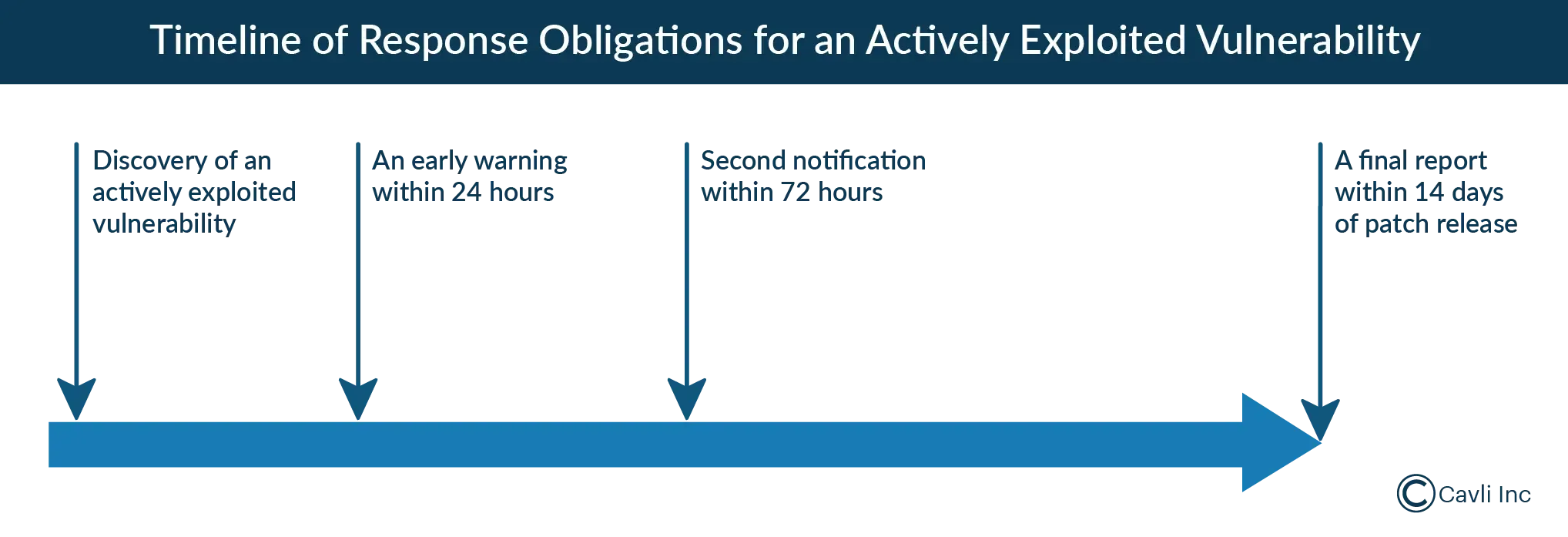
First Vulnerability Warning
An early warning must be submitted within 24 hours of becoming aware of an actively exploited vulnerability or severe incident.
Follow-up
A full notification must be submitted within 72 hours with detailed information on affected devices, versions, and their mitigation status.
Final Report
The detailed report should be presented within 14 days after a corrective measure is available for actively exploited vulnerabilities, and within one month for severe incidents.
Coordinated Vulnerability Disclosure Policy (CVD Policy)
The EU Cyber Resilience Act (EU CRA) mandates implementing a Coordinated Vulnerability Disclosure (CVD) policy to enhance cybersecurity within the European Union, particularly for products such as IoT devices. CVD refers to the process of responsibly disclosing security vulnerabilities to ensure they are properly addressed before malicious actors can exploit them. Key Points on CVD under the CRA regulation are:
Vulnerability Disclosure Requirement
The EU CRA regulation requires manufacturers to have a clear Coordinated Vulnerability Disclosure policy in place. Here, the vulnerabilities discovered in products are reported in a controlled manner to allow for timely fixes and patches, protecting end-users and preventing exploitation.
Role of Manufacturers
Manufacturers must provide mechanisms for securely receiving vulnerability reports from researchers, security experts, or the public.
Disclosure to Authorities (ENISA)
Critical vulnerabilities and active incidents must be disclosed through the CRA Single Reporting Platform to the relevant CSIRT, with the information made available to ENISA, within 24 hours for an early warning and followed by a full notification within 72 hours.
Collaboration Between Stakeholders
CVD facilitates collaboration between manufacturers, security researchers, and government bodies. This coordinated approach ensures that vulnerabilities are addressed transparently and efficiently, minimizing the risk to end users.
Public Transparency
Once a vulnerability is fixed, manufacturers must make the relevant information public, ensuring transparency. This process is important for building trust and allowing users and organizations to take proactive measures.
CSIRT
Under the EU CRA regulation, manufacturers are required to report security vulnerabilities and actively exploited vulnerabilities through the CRA Single Reporting Platform to the relevant CSIRT, with ENISA also involved in the reporting architecture.
CSIRTs are integral to this process. A Computer Security Incident Response Team (CSIRT) is a team of cybersecurity experts that handles and responds to cybersecurity incidents, including potential and active threats. It is responsible for detecting, managing, mitigating, and recovering from cyber incidents. They often coordinate with other cybersecurity bodies and agencies, such as ENISA, to ensure that cyber incidents are appropriately managed and reported.
Conformity Assessment
Determine whether the product falls under the default, important, or critical category under the CRA, as this affects whether self-assessment or notified-body involvement is required.
Conformity Assessment Pathways
- Default Category: For non-critical products, manufacturers can self-assess and issue an EU Declaration of Conformity.
- Important Products:
- Class I (no standards applied): Must undergo mandatory external assessment by a Notified Body.
- Class I (standards applied): Self-assessment allowed if using harmonized standards.
- Class II: Requires mandatory external assessment.
- Critical Products: All critical products must undergo mandatory external assessment by a Notified Body.
Transparency & User Trust
- Ensure transparency about the product's security features by providing clear and accessible documentation that highlights the security measures taken, product risks, and maintenance obligations.
Post-Market Support
- Provide post-market security updates through the declared support period, which should generally be at least five years unless the product is expected to be used for less than five years. Thus, ensuring these updates are separate from functional upgrades to avoid confusion.
- Enable secure over-the-air updates to ensure devices can be updated without exposing them to additional risks.
CRA Implications for End Users
The EU Cyber Resilience Act (CRA) improves security for end users of connected products by ensuring manufacturers meet strict cybersecurity standards. It mandates that devices are built securely, with clear usage instructions and regular security updates. The CRA also requires manufacturers to disclose vulnerabilities, keeping users informed about potential risks. This strengthens trust in digital products, reducing the likelihood of cyberattacks and ensuring long-term protection.
How Cavli Wireless is working toward CRA compliance
At Cavli Wireless, we are fully committed to achieving CRA compliance. We are actively aligning our cellular IoT modules, categorized as critical products under the Cyber Resilience Act (CRA), with the required cybersecurity standards. Depending on the final product categorization and conformity pathway, we are undergoing comprehensive assessments and implementing proactive measures to mitigate potential threats, while ensuring that any vulnerabilities are swiftly reported, tracked, and addressed. To enhance transparency, we are streamlining our product documentation, making it easily accessible to both customers and regulatory bodies. In addition, we are dedicated to providing ongoing security updates for our IoT module. As we work towards full compliance by December 2027, we are also ensuring our hardware and software solutions consistently meet the highest cybersecurity standards for high-risk products, in alignment with the EU CRA regulation.
Conclusion
The EU Cyber Resilience Act marks a fundamental shift in how IoT devices are designed, deployed, and maintained. Cybersecurity is no longer an afterthought or a value-add—it is now a regulatory requirement embedded into the product lifecycle.
For IoT manufacturers, this means moving beyond reactive security measures toward a secure-by-design approach, where risk assessment, vulnerability management, and continuous updates are built into every stage of development. From firmware integrity to long-term software support, compliance with EU CRA regulation is as much about process maturity as it is about technology.
The challenge is not just meeting compliance deadlines, but adapting to a new operating model where devices must remain secure throughout their lifecycle, across geographies, networks, and evolving threat landscapes.
Those who act early will not only avoid regulatory risks but also gain a competitive advantage by building trust, reliability, and long-term resilience into their IoT solutions. In the IoT market, where security is becoming a differentiator, CRA compliance is no longer just about regulation; it’s about future-proofing your IoT business.





